Information Security Policy
Effective from: 1st January 2026
1. Purpose
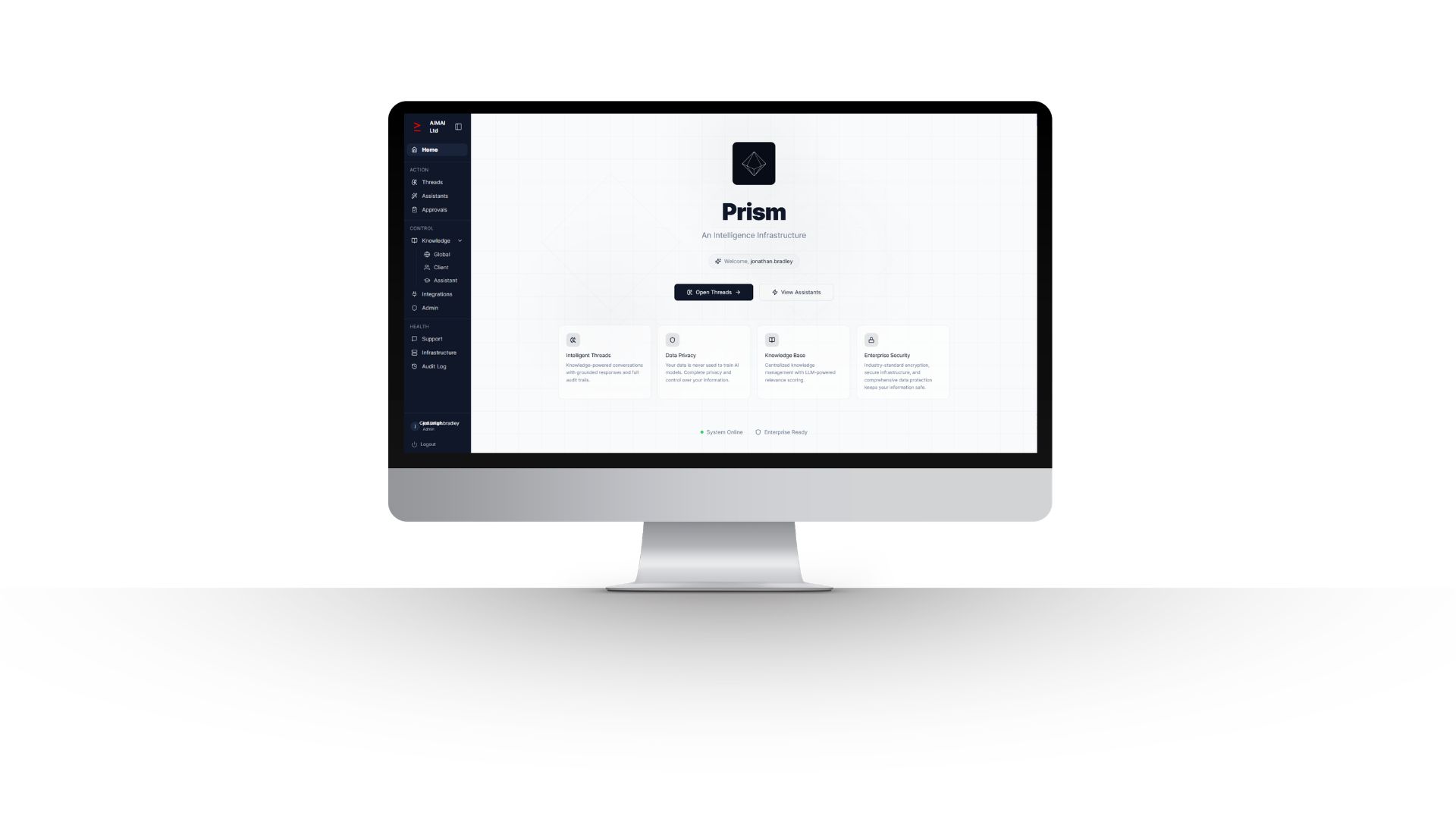
This Information Security Policy sets out how AIMAI Ltd protects information, systems, services and operational workflows across the business and within PRISM. The purpose of this policy is to preserve the confidentiality, integrity and availability of company and client information, support safe and governed AI usage, reduce operational and regulatory risk, and ensure that PRISM is operated in a secure, controlled and auditable manner.
2. Scope
This policy applies to AIMAI Ltd personnel, contractors, authorised users, client users, administrators, partners and any third party with authorised access to AIMAI systems or PRISM environments.
It covers company and client data, shared workspaces, client-level workspaces, threads, knowledge bases, approvals, audit records, custom assistants, integrations, workflow tools, supporting infrastructure, development activity, support activity, and operational processes used to deliver or maintain PRISM and associated AIMAI services.
3. Security Principles
- Security shall be built into the design, deployment and operation of AIMAI services.
- Access shall be granted on a least-privilege and role-based basis.
- Client environments and client information shall be appropriately separated.
- AI use shall be governed by policy, approved knowledge and human oversight.
- Information shall only be accessed, processed or shared for authorised business purposes.
- Security controls, workflows and governance content shall be reviewed and improved continuously.
- Material activity affecting system integrity, access, decisions or usage should be auditable.
4. Roles and Responsibilities
AIMAI Ltd is responsible for establishing and maintaining appropriate security controls across its services and operations. The policy owner is jonathan.bradley, who is responsible for overseeing this policy and ensuring it remains current.
Administrators and authorised internal personnel are responsible for managing user access, permissions, configuration, operational oversight and secure change activity. All users are responsible for protecting credentials, using services lawfully and appropriately, following approved processes, and reporting suspected incidents, misuse or weaknesses without delay.
5. Information Classification and Handling
AIMAI information and client information shall be handled according to its sensitivity, business value, client obligations and legal or regulatory requirements. Information may be classified, where appropriate, as public, internal, confidential or restricted.
Confidential or restricted information must only be accessed by authorised users with a legitimate business need. Information must not be copied, exported, shared or retained outside approved environments except where explicitly authorised and appropriately controlled.
6. Access Control and Identity Management
Access to AIMAI systems and PRISM shall be controlled through authorised user accounts, permissions and administrative controls. Access rights shall be allocated according to role and legitimate business need, and removed or amended promptly when no longer required.
- Users must keep credentials confidential and must not share accounts.
- Administrative access shall be restricted to authorised personnel.
- Permissions should reflect the minimum access required to perform a role.
- Access to client-level workspaces, knowledge and threads shall be limited to the correct authorised users.
- External or partner access shall be controlled through designated groups and permissions.
7. Platform and Infrastructure Security
PRISM is operated on Amazon Web Services infrastructure. Current core infrastructure and supporting services include AWS EC2, RDS, S3, SES, SNS and CloudWatch. These services support hosting, database, storage, email, SMS and monitoring functions.
AIMAI operates dedicated infrastructure for client environments within PRISM to support stronger separation, clearer boundaries and safer deployment in governance-sensitive contexts. Core platform capabilities including user management, logging, workflow engine and API layer are developed and operated in-house on AWS infrastructure.
8. Encryption and Secure Transmission
Data transmitted to and from PRISM and related services shall be protected using SSL/TLS. AIMAI uses Let’s Encrypt for SSL certificate issuance. Secure transmission controls are used to reduce the risk of interception, tampering or unauthorised exposure of data in transit.
AIMAI will apply reasonable and appropriate security controls to protect stored data and supporting systems, taking account of system design, provider capabilities, sensitivity of data and operational requirements.
9. AI and Model Governance
AIMAI uses third-party AI and machine learning providers as part of service delivery and PRISM functionality. Current providers include OpenAI for general LLM processing, Anthropic for LLM processing, Google for Imagen image generation, and Deepgram for audio transcription and speech processing.
AI outputs must not be treated as automatically correct or relied upon without appropriate human review where there is operational, legal, financial, regulatory or client impact. AIMAI uses a governed AI approach, meaning AI usage is bounded by policies, controls, approved knowledge and defined workflows rather than ad hoc use.
AIMAI continuously evaluates emerging AI capabilities and may adopt additional providers or models over time where appropriate. Any new sub-processors will be disclosed accordingly.
10. Knowledge Governance in PRISM
PRISM includes knowledge governance features designed to improve consistency, oversight and control. The PRISM Knowledge Base acts as a structured source of approved business knowledge so that assistants and threads can work from aligned context rather than informal or inconsistent inputs.
Approvals functionality enables proposed knowledge to be reviewed and published only by authorised roles. Threads provide shared workspaces so work remains visible, repeatable and grounded in approved knowledge. Client-level knowledge and client-level threads support cleaner separation between clients and reduce cross-contamination risk.
Audit records support evidence of how intelligence was used, what context was relied on, and what was produced. Admin management, partner access and in-built support features help maintain control as usage scales across internal and external users.
11. Secure Development and Change Management
AIMAI uses GitHub for source code hosting and deployment activity. Secure development and operational change shall follow AIMAI’s delivery and operating model of assess, design, deploy and iterate.
Changes to systems, configurations, prompts, workflows, knowledge structures, assistants and policies should be implemented in a controlled manner, with appropriate review, testing and oversight relative to the level of risk and impact. Continuous iteration is part of AIMAI’s operating model, but changes must still preserve security, governance and service integrity.
12. Logging, Monitoring and Audit
AIMAI maintains monitoring and operational oversight appropriate to its services and infrastructure. AWS CloudWatch is used as part of the monitoring stack. Logging and audit mechanisms are used to support service integrity, incident detection, troubleshooting, governance and evidencing of relevant activity.
Monitoring, logs and audit records shall be accessed only by authorised personnel and used for legitimate operational, security, governance or legal purposes.
13. Incident Management
AIMAI will maintain processes for identifying, assessing, containing, investigating and responding to security incidents, suspected breaches, misuse, weaknesses or service-affecting events.
- Users must report suspected security incidents or weaknesses without delay.
- AIMAI will investigate incidents and take appropriate containment and remediation steps.
- Access, systems, workflows or integrations may be restricted or suspended where necessary to reduce risk.
- Where required by law, contract or regulatory obligation, AIMAI will make appropriate notifications.
- Lessons learned should inform future improvements to controls, processes and governance content.
14. Third-Party Suppliers and Sub-processors
AIMAI relies on selected third-party providers to support service delivery. Current providers include:
- Amazon Web Services, EC2, RDS, S3, SES, SNS and CloudWatch, for hosting, database, storage, email, SMS and monitoring
- OpenAI, for general LLM processing
- Anthropic, for LLM processing
- Google, for Imagen image generation
- Deepgram, for audio transcription and speech processing
- GitHub, for source code hosting and deployment
- Fasthosts, for DNS management
- Let’s Encrypt, for SSL certificate issuance
- Stripe, for payment processing, planned
Third-party connectors, including examples such as Sage 50, CRM systems and accounting platforms, may be integrated on a client-by-client basis and will be disclosed as applicable to the relevant engagement.
AIMAI will take reasonable steps to select and manage suppliers in a way that supports secure delivery, lawful processing and appropriate governance.
15. Business Continuity and Resilience
AIMAI will operate PRISM and supporting services with resilience and continuity in mind, taking account of infrastructure design, service dependencies, operational support and restoration needs. Security, availability and continuity considerations should be reflected in platform design, deployment choices, monitoring and incident response.
AIMAI will review resilience arrangements over time as the platform, supplier landscape and client usage evolve.
16. Privacy, Data Protection and International Transfers
AIMAI processes personal data in accordance with applicable data protection obligations and its published privacy documentation. Depending on the circumstances, AIMAI may act as a controller or processor.
PRISM may involve personal data across identity data, account and access data, communications, workspace content, usage data and integrated system data. AIMAI applies access controls, environment separation, permissions, monitoring and secure transmission measures to support data protection.
Where personal data is transferred internationally, AIMAI uses appropriate safeguards, including the UK International Data Transfer Agreement or the UK Addendum to the EU Standard Contractual Clauses, where applicable.
17. Acceptable Use and User Obligations
- Users must use AIMAI systems and PRISM only for authorised, lawful and legitimate business purposes.
- Users must not attempt unauthorised access, probing, misuse, reverse engineering, malware distribution, overload attacks or other activity that could compromise systems or data.
- Users must not upload, process or share content they are not authorised to use.
- Users must protect passwords and access credentials and must not disclose them improperly.
- Users must not rely on AI outputs without suitable human review where there is any material impact.
- Users must report suspected misuse, security incidents, breaches or weaknesses promptly.
18. Awareness, Review and Policy Maintenance
AIMAI will maintain this policy as a living document and review it periodically, and whenever there are material changes to the business, platform, supplier landscape, legal obligations or risk profile.
Relevant personnel should be made aware of their information security responsibilities. Governance content, workflows and policy structures used within PRISM may also be updated over time to reflect operational learning, evolving risks and improved controls.
19. Contact Details
AIMAI Ltd
Office 18, The Globe Innovation Centre
Slaithwaite
HD7 5JN
01484 767892
info@aimai.co.uk