Incident and Data Breach Response Policy
Effective from: 1st January 2026
This policy sets out how AIMAI Ltd identifies, reports, assesses, contains, investigates, notifies, and resolves security incidents and personal data breaches affecting its services, systems, personnel, and client environments.
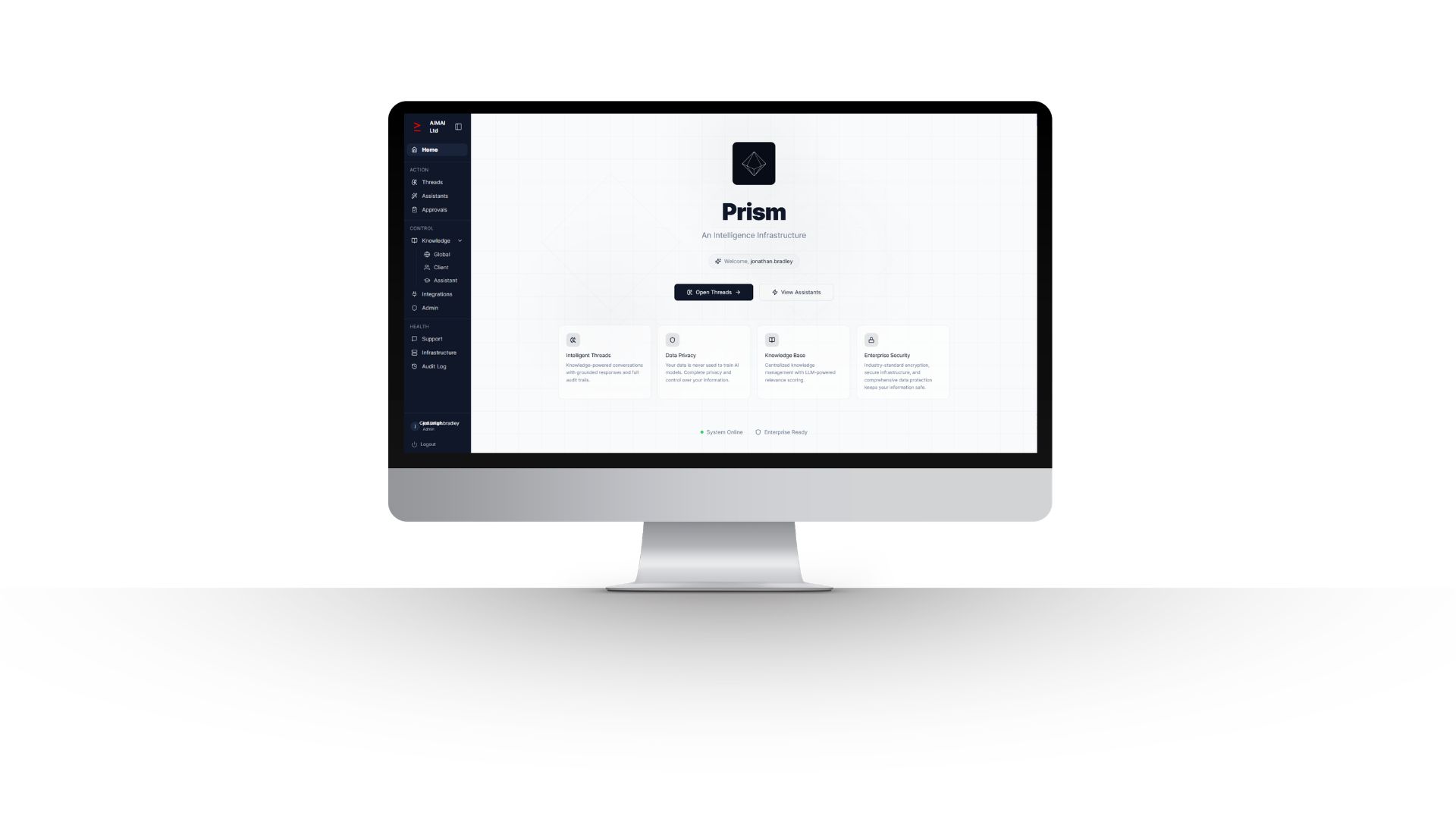
This policy applies to AIMAI personnel, contractors, authorised users, and relevant third parties across AIMAI websites, PRISM platform environments, AI assistants, threads, knowledge features, approvals, audit functionality, integrations, and supporting infrastructure.
1. Definitions
For the purposes of this policy, a security incident is any actual or suspected event that compromises, or may compromise, the confidentiality, integrity, or availability of information, systems, services, credentials, or operational processes. A personal data breach is a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to, personal data. Not every security incident is a personal data breach, but every suspected personal data breach must be treated as a priority incident.
2. Roles and responsibilities
- Policy owner: jonathan.bradley is responsible for maintaining this policy and overseeing its review.
- AIMAI leadership: responsible for supporting incident response decisions, resourcing, escalation, and external communications where required.
- Platform administrators and authorised technical personnel: responsible for monitoring, triage, containment, investigation, remediation, logging, and recovery actions.
- Personnel, contractors, and authorised users: must report suspected incidents, breaches, misuse, weaknesses, or unusual activity without delay.
- Third-party providers and sub-processors: are expected to operate appropriate controls within their own environments and to notify AIMAI where incidents affecting AIMAI data or services arise, in line with applicable terms.
3. Response principles
- Respond quickly and proportionately to reduce harm.
- Prioritise containment, evidence preservation, service stability, and protection of client and personal data.
- Apply least-privilege access controls and restrict access further where required during an incident.
- Maintain appropriate records so actions, decisions, timelines, and evidence are auditable.
- Escalate promptly where legal, contractual, operational, or reputational risk may arise.
- Notify affected parties and regulators when required by applicable law or contractual commitments.
- Use each incident as an input to security, governance, and operational improvement.
4. Identification and reporting
Incidents may be identified through monitoring, logging, audit records, platform behaviour, user reports, third-party notifications, or routine operational review. AIMAI uses AWS services including EC2, RDS, S3, SES, SNS, and CloudWatch as part of its infrastructure and monitoring approach. Suspected incidents must be reported internally without delay as soon as they are observed or suspected. Reports should include, where known, the nature of the issue, affected systems or data, date and time identified, who identified it, and any immediate actions already taken.
5. Triage and classification
On receipt of a report, AIMAI will assess the incident promptly to determine its nature, credibility, urgency, and potential impact. Classification will consider whether personal data may be involved, whether the event affects confidentiality, integrity, or availability, whether client environments are affected, whether there is evidence of unauthorised access or disclosure, and whether third-party providers or integrations may be implicated. Incidents assessed as likely to involve personal data, client impact, significant service disruption, material security weakness, or regulatory risk must be escalated immediately.
6. Containment
- Disable or restrict affected accounts, credentials, tokens, sessions, keys, integrations, or services where necessary.
- Isolate affected systems, workloads, storage locations, endpoints, or workflows to limit spread or ongoing exposure.
- Block malicious traffic, suspicious access routes, or unauthorised processes where possible.
- Preserve logs, audit records, system metadata, and other relevant evidence.
- Coordinate with relevant sub-processors or hosting providers where their services may be involved.
- Take proportionate steps to maintain critical service continuity where safe to do so.
7. Investigation and assessment
AIMAI will investigate the incident to establish what happened, when it began, how it was detected, which data, systems, users, or clients may be affected, whether data was accessed, altered, lost, or disclosed, whether the issue remains ongoing, and what root causes or contributing factors are present. Where personal data may be involved, AIMAI will assess the categories of data, approximate number of data subjects and records affected where known, likely consequences for affected individuals, and whether the breach is likely to result in a risk, or a high risk, to the rights and freedoms of natural persons.
8. Notification and escalation
Where AIMAI acts as a controller and becomes aware of a personal data breach that is likely to result in a risk to individuals, AIMAI will notify the Information Commissioner’s Office without undue delay and, where required, within 72 hours of becoming aware of it. Where a breach is likely to result in a high risk to individuals, AIMAI will also communicate the breach to affected individuals without undue delay unless an exemption applies. Where AIMAI acts as a processor on behalf of a client, AIMAI will notify the relevant client without undue delay after becoming aware of a personal data breach affecting data processed for that client, providing available information to support the client’s own assessment and notification obligations.
- Notifications should be clear, accurate, and based on verified information available at the time.
- Initial notifications may be supplemented as more information becomes available.
- AIMAI may also notify insurers, legal advisers, law enforcement, affected partners, or other stakeholders where appropriate and justified by the circumstances.
- Public statements or external communications must be controlled to avoid inaccurate or premature disclosure.
9. Recovery and remediation
Following containment and assessment, AIMAI will take appropriate remediation steps to remove the cause of the incident, reduce the likelihood of recurrence, and restore affected services and data safely. This may include credential resets, access reviews, patching, configuration changes, code fixes, restoration from backups, workflow changes, policy updates, additional monitoring, retraining of personnel, or changes to supplier or integration controls. Restoration of service must be managed carefully to avoid reintroducing compromise or data integrity issues.
10. Record keeping
AIMAI will maintain records of relevant incidents and personal data breaches, including the facts relating to the incident, its effects, the assessment carried out, actions taken, notification decisions, communications issued, remediation steps, and closure outcomes. These records support accountability, auditability, legal compliance, operational learning, and evidence of appropriate handling.
11. Third-party services and sub-processors
AIMAI uses third-party infrastructure and service providers as part of its service delivery, including AWS, OpenAI, Anthropic, Google for image generation, Deepgram, GitHub, Fasthosts, Let’s Encrypt, and Stripe as a planned payment processor. Third-party connectors, such as Sage 50, CRM systems, and accounting platforms, may also be used on a client-by-client basis and will be disclosed as applicable per engagement. Where an incident involves or may involve a third-party provider, AIMAI will coordinate investigation and response with that provider as appropriate while continuing to manage its own legal, contractual, and client communication responsibilities.
12. Awareness and reporting culture
Relevant personnel must understand their responsibility to identify and escalate suspected incidents promptly. Delayed reporting increases risk and may affect legal notification deadlines. AIMAI will support awareness of security, acceptable use, access control, governance, and incident reporting expectations as part of its wider information security and responsible AI framework.
13. Review and maintenance
This policy is a living document and will be reviewed periodically, and whenever there is a material change to AIMAI’s business, platform, supplier landscape, legal obligations, security posture, or risk profile, or following a significant incident or breach. AIMAI may update related procedures, controls, and supporting governance documentation to reflect operational learning and emerging best practice.
14. Contact
AIMAI Ltd
Office 18, The Globe Innovation Centre
Slaithwaite, HD7 5JN
Telephone: 01484 767892
Email: info@aimai.co.uk