ACCEPTABLE USE POLICY
Effective from: 1st January 2026
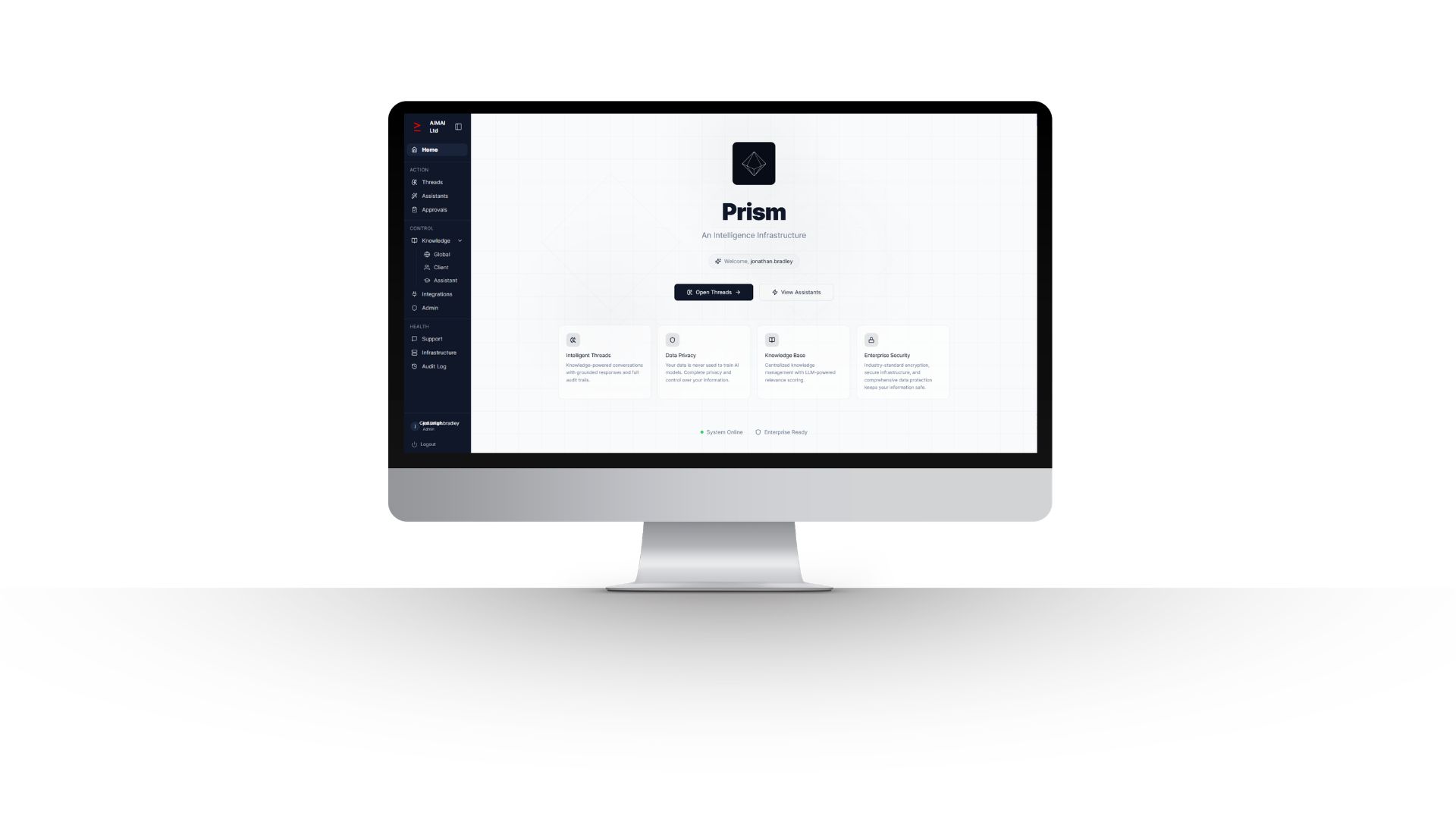
This Acceptable Use Policy sets out the rules for using AIMAI Ltd websites, platforms, services, workspaces, assistants, integrations and related systems, including PRISM and any associated client environments. By accessing or using these services, you agree to comply with this policy.
1. Definitions
For the purposes of this policy:
- AIMAI means AIMAI Ltd.
- Services means AIMAI’s websites, platform environments, AI assistants, threads, integrations, tools and related systems.
- User means any individual accessing or using the Services, whether as a client, employee, contractor, partner or authorised third party.
- Client Data means any information, files, prompts, records, documents, communications or other material submitted to or processed through the Services.
- Organisation means the client, business or entity on whose behalf a User is accessing the Services.
2. Purpose
The purpose of this policy is to ensure that the Services are used lawfully, securely, responsibly and in a way that protects AIMAI, its clients, their users and all related data, systems and infrastructure.
3. Scope
This policy applies to all Users of the Services and to all access, use, uploads, prompts, outputs, integrations, data handling and interactions carried out within or through the Services.
4. Permitted Use
Users may use the Services only for legitimate business purposes that have been properly authorised.
- Use the Services in accordance with applicable law, regulation and contractual obligations.
- Use the Services only within the access rights, permissions and client context assigned to you.
- Submit and process only data that you are authorised to use.
- Use outputs as part of governed business workflows, with human review where required.
- Follow all internal organisational rules relating to confidentiality, information security, privacy, compliance and records management.
- Report suspected misuse, errors, incidents or breaches without delay.
5. Prohibited Use
Users must not use the Services to do any of the following:
- Break any applicable law, regulation, duty or court order.
- Submit, generate, store, share or distribute unlawful, defamatory, fraudulent, abusive, discriminatory, obscene or misleading content.
- Infringe any intellectual property, confidentiality, privacy or other legal rights.
- Upload or process data without proper authority or lawful basis.
- Attempt to access data, accounts, workspaces, threads, assistants or systems that you are not authorised to access.
- Circumvent permissions, controls, authentication measures, usage restrictions or security protections.
- Probe, scan, test or exploit vulnerabilities without explicit written authorisation.
- Introduce malware, ransomware, malicious code, harmful scripts or any other hostile or disruptive material.
- Use the Services to spam, scrape, harvest data improperly, overload systems or interfere with performance or availability.
- Reverse engineer, copy, replicate, benchmark for competitive purposes or attempt to build competing infrastructure, products or services from the Services.
- Use the Services to make fully automated decisions where human review is legally, contractually or operationally required.
- Misrepresent AI-generated content as independently verified fact where it has not been reviewed.
- Use the Services in any way that could cause reputational, operational, legal or security harm to AIMAI, its clients or other users.
6. Data Handling and Confidentiality
Users must handle all Client Data and other confidential information with appropriate care and only for authorised purposes. Users must not disclose confidential information to unauthorised persons or use it outside the permitted scope of the relevant engagement or workflow.
The Organisation retains ownership of its data. AIMAI processes data for service operation and delivery. Data must not be extracted, copied or shared outside authorised environments except where this is expressly permitted and properly controlled.
Users must not enter personal data, special category data, commercially sensitive data or regulated information into the Services unless they are authorised to do so and appropriate controls are in place.
Data is not sold, shared or used for model training beyond service operation. Users must not attempt to access, combine or infer data belonging to another client, workspace or user.
7. Security and Access Control
- Users must keep login credentials confidential and must not share accounts.
- Users must use strong passwords and any required multi-factor authentication.
- Users must access the Services only through approved methods, devices and networks.
- Users must not disable logging, monitoring, audit controls or security safeguards.
- Users must notify the relevant internal owner immediately if credentials are lost, compromised or suspected to be compromised.
- Access rights must be based on role, business need and authorised scope.
8. Responsible Use of AI
AI outputs may be useful but are not infallible. Users remain responsible for reviewing, validating and approving outputs before relying on them in business, operational, legal, financial, regulatory or client-facing contexts.
- Do not treat AI outputs as automatically correct, complete or suitable for use without review.
- Apply human judgement, especially where outputs affect customers, clients, compliance, finance, legal matters or risk decisions.
- Do not use prompts or instructions designed to override governance controls, misuse the system or generate harmful content.
- Use the Services in line with your Organisation’s approved policies, playbooks and escalation requirements.
9. Audit, Monitoring and Records
Use of the Services may be logged, monitored and reviewed for security, quality assurance, operational improvement, compliance, incident investigation and governance purposes. This may include records of prompts, outputs, users, timestamps, access events, approvals and related activity.
By using the Services, Users acknowledge that such monitoring and record keeping may take place where lawful and appropriate.
10. Third-Party Infrastructure and Processing
AIMAI operates its services using a combination of in-house systems and approved third-party providers. Current infrastructure and processing providers include:
- Amazon Web Services (AWS): EC2, RDS, S3, SES, SNS and CloudWatch for hosting, databases, storage, email, messaging and monitoring.
- OpenAI: general large language model processing.
- Anthropic (Claude): large language model processing.
- Google (Imagen): image generation.
- Deepgram: audio transcription and speech processing.
- GitHub: source code hosting and deployment.
- Fasthosts: DNS management.
- Let’s Encrypt: SSL certificate issuance.
- Stripe: planned payment processing provider, if and when payment functionality is activated.
Third-party connectors, including accounting systems, CRM platforms and other external business tools, may be enabled on a client-by-client basis and will be disclosed as applicable for the relevant engagement.
AIMAI continuously evaluates emerging AI capabilities and may adopt additional providers or models over time. Any new sub-processors will be disclosed accordingly.
User management, logging, workflow orchestration, API services and related application layers are developed and operated in-house on AWS infrastructure.
11. Enforcement
AIMAI and the relevant Organisation may investigate suspected breaches of this policy. Where a breach is identified or reasonably suspected, access may be restricted, suspended or removed immediately.
AIMAI may also remove content, disable integrations, preserve evidence, notify relevant parties and take any other proportionate action necessary to protect the Services, users, clients, data or legal position.
12. Reporting Misuse and Security Incidents
Users must report any actual or suspected misuse, unauthorised access, data breach, confidentiality issue, security incident, policy violation or harmful output through the Organisation’s designated internal reporting route without delay.
13. Review and Updates
This policy may be updated from time to time to reflect changes in law, regulation, technology, infrastructure, services or operational requirements. The latest published version will apply from the date it is posted.